The outdoor industry landscape is changing, and we’re here to help with timely insights to grow your brand. Discover the trends that defined outdoor retail sales last year in our new report.
Continue readingBlack History Month: Celebrating Black Leaders in the Outdoors
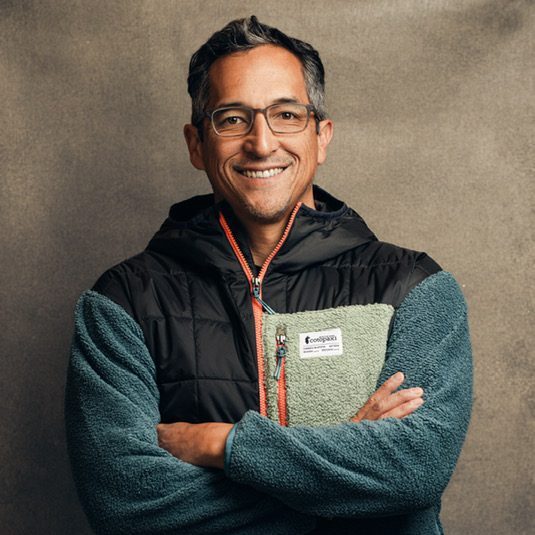
Welcome Damien Huang, CEO of Cotopaxi, to the OIA Board
2023 Thrive Outside Days
Thanks to Thrive Outside community leaders, partners, and participants, our 2023 Thrive Outside Day events were an overwhelming success! Read and see below how a few of the 13 Thrive Outside Communities across the country created an array of new opportunities for children, youth, and their families to enjoy the outdoors – helping to build new connections and encourage year-round outdoor experiences.
Oklahoma City

At the Oklahoma City Thrive Outside Day, youth kayakers representing the Boys and Girls Club of Oklahoma County and the Oklahoma City Indian Clinic demonstrated their kayaking skills in front of 3,800 attendees cheering from the banks of the Oklahoma River. The weekend of fun included A Most Beautiful Thing Inclusion Fund (AMBTIF) award ceremony, with AMBTIF founder Arshay Cooper and Olympians welcoming and inspiring 55 youth to embrace the healing power of watersports. Youth rowers representing six middle schools then rowed in their first race with over 4,000 spectators in attendance.
St. Louis

“This is what community looks like” – Thrive Outside Day Participant
In St. Louis, River City Outdoors, O’Fallon Park YMCA, The Boys and Girls Club of Greater St. Louis, and Cherokee Recreation Center all partnered to offer activities for Thrive Outside Day. Over 150 participants were able to enjoy a mobile climbing wall, a community BBQ, and a giveaway of River City Outdoor swag.
Detroit

With support from Wilderness Inquiry, over 300 Detroit students and community members had the opportunity to paddle in canoes on the inland lakes of Belle Isle Park and engage in land-based environmental education activities with other partner organizations and agencies. The Canoemobile
visit marked the beginning of Detroit’s Thrive Outside Days, a month-long embrace of making time to go outside and connect with nature and one another.
The team also curated and promoted a weekly list of ways to get outside and thrive all through October with other members of the local network. Detroit’s Thrive Outside Days culminated with a Mountain Bike Ramble event at Rouge Park in Detroit, where the students of the Hamtramck High Schools Outdoor Adventure Club spent the day riding the trails.
Grand Rapids
“Thrive Outside Day in Grand Rapids was a chance to celebrate our community, give away some free gear and swag, and invite folks to come and get familiar with our Gear Library.” – Sam Truby, Gear Library Supervisor
The Grand Rapids team observed that while lending equipment and clothing on a temporary basis is a great way to make outdoor activities possible for children, youth, and families who need it, “giving someone gear to keep creates a sense of excitement that a temporary item does not. This event showed that gear giveaways could be a potential ongoing activity at the gear library, as it gives winners a sense of ownership of the activities they do outside.”
New Analysis Reveals Strength of the Outdoor Economy
Today, the U.S. Bureau of Economic Analysis (BEA) released new data showcasing the tremendous impact of outdoor recreation on America’s economy. In 2022, the BEA found that outdoor recreation accounted for $1.1 trillion in gross economic output, 2.2% of gross domestic product (GDP), and supported 5 million jobs across the United States.
“It comes as no surprise that outdoor recreation and the outdoor economy continue to demonstrate outstanding growth, which also supports the historic trends in outdoor participation we have seen in recent years,” said OIA President Kent Ebersole. “The outdoor recreation participant base grew for the eighth consecutive year to a record 168.1 million participants, and new participants are increasingly diverse and looking to businesses to lead on sustainability, equity, and conservation. This new data demonstrates the strength of the outdoor recreation industry and our collective power to drive sustainable economic growth while protecting – and growing access to – the benefits of the outdoors for everyone.”
BEA launched its outdoor recreation economy project in 2017 to “deepen the public’s understanding of the economic impact of outdoor recreation, inform decision making, and improve governance and long-term management of public lands and waters.”
Explore the power of the outdoor recreation economy through our interactive map, which now lists state-level participation data alongside jobs, wages, and total economic value.
Meet the New and Returning OIA Board Members
PFAS Phase-Out: 5 Key Steps for Your Outdoor Brand
By James Pollack, OIA Clean Chemistry and Materials Coalition Legislative Advisor, Attorney at Marten Law
Start your brand’s journey to eliminating per- and polyfluoroalkyl substances (PFAS), also known as Forever Chemicals.
You have probably started hearing a lot about PFAS, a large, complex group of synthetic chemicals found in various everyday consumer products like water-resistant clothing and cookware. A combination of regulatory requirements and consumer demand has created growing pressure on sectors worldwide to achieve PFAS elimination. States have proposed hundreds of potential laws and regulations targeting PFAS in a variety of consumer products. Many of these laws will impact outdoor brands that have used PFAS for durability as well as water and stain resistance. Intimidated? Don’t be. Together, we can replace existing products with more sustainable alternatives to provide customers with products that are just as reliable and durable.
1). Assemble your PFAS team
First and foremost, you have to build a dedicated team to effectively tackle PFAS phase-out. For the most comprehensive and holistic approach, I recommend bringing together a diverse group with a multiplicity of perspectives and expertise. While a chemicals expert may understand what needs to change about your product’s material composition, a designer will have insight into how materials fit into the product, marketing will help articulate why and how your outdoor brand is evolving its product, and sales will have to communicate the transition to buyers and consumers alike. Once you have a team assembled, appoint a champion who will take ownership of the initiative and lead it to fruition.
2). Understand the timeline for PFAS legislation
As PFAS chemicals are generally a state legislative issue for the time being, your brand will have to navigate different states with different deadlines for phase-out and elimination. For example, California’s ban on PFAS in textile articles goes into effect January 1, 2025, Vermont’s ban on all PFAS in food packaging, ski wax, and after-market fabric treatments goes into effect on July 1, 2024, and Minnesota’s ban on the sale of cookware, fabric treatments, juvenile products, ski wax, and food packaging with intentionally added PFAS goes into effect on January 25, 2025.
Once you have a grasp on the state regulations that apply to your product categories, it is important to align your product development cycle with upcoming regulatory deadlines.
Pro Tip: CCMC members have access to a constantly updated Regulatory Tracker to ensure members are aware of new and evolving deadlines around PFAS and other harmful chemicals.
3). Work with your suppliers on a PFAS phase-out plan
After aligning your product development cycle with your state’s regulatory timeline, you should work to communicate key deadlines with your suppliers. There’s a good chance that your suppliers are addressing similar requests from other brands and distributors, so leverage their expertise. Ask them about the alternatives to PFAS they’ve been using and the options that exist for sustainable material evolution.
4). Draw on expertise within the outdoor industry
The outdoor industry has a long history of working together to catalyze broader change and drive innovation. As catalysts, we know that we go farther, and faster, when we work together. In addition to your suppliers, you can leverage the expertise of lawyers, labs, consultants, and other outdoor brands to crystalize your PFAS phase-out strategy.
OIA’s Clean Chemistry and Materials Coalition is designed to support retailers, brands, manufacturers, and distributors in a way that is unique to their PFAS phase-out stage. We provide our members with scalable action plans for eliminating and replacing harmful chemicals and materials, delivering supply chain transparency, addressing recycling and emissions disclosures, and more. CCMC members also gain access to a community network of other brands working on the same challenges, and technical and legislative advisors (like myself) who are here to offer support. For more insight into how CCMC can support your brand, watch our introductory webinar.
5). Design and implement your ongoing PFAS and chemical compliance efforts
The last step, of course, is execution. Now that you have a team, a timeline, and a supportive community of peers and experts, it is time to begin the process of altering your products and supply chain to ensure they are compliant with a variety of state sustainability regulations. This may include steps like testing your product’s material composition, obtaining appropriate certifications, and implementing a restricted substance list. It is important to ensure that all your outdoor brand’s products meet regulatory requirements, so I recommend establishing inventory management practices to track different products’ PFAS phase-out life stages.
The path towards PFAS elimination is not linear–nor easy–but if we take one step at a time and work together, we can be catalysts for sustainable growth. If you’re looking for more robust support and a community to lean on, join me and the Clean Chemistry and Materials Coalition.
About James Pollack
 James Pollack is an attorney at Marten Law based in Seattle, WA, whose practice focuses on consumer product regulatory compliance, emerging contaminants, and environmental review. James leads the firm’s consumer products regulatory practice and helps consumer product manufacturers in a wide array of industries that are working to understand the complicated and shifting regulatory and litigation environments surrounding emerging contaminants. He has extensive knowledge on PFAS regulatory compliance at the federal and state level. James’s clients include textile and apparel manufacturers, outdoor recreational product manufacturers, food product manufacturers, and retailers. He also works with industry associations to update membership on regulatory developments.
James Pollack is an attorney at Marten Law based in Seattle, WA, whose practice focuses on consumer product regulatory compliance, emerging contaminants, and environmental review. James leads the firm’s consumer products regulatory practice and helps consumer product manufacturers in a wide array of industries that are working to understand the complicated and shifting regulatory and litigation environments surrounding emerging contaminants. He has extensive knowledge on PFAS regulatory compliance at the federal and state level. James’s clients include textile and apparel manufacturers, outdoor recreational product manufacturers, food product manufacturers, and retailers. He also works with industry associations to update membership on regulatory developments.
Read more from James on PFAS:
Can Orange Juice Claim to be Green?
PFAS in Consumer Products are Targeted by State Regulators and Class Action Plaintiffs
What Is in EPA’s Billion Dollar PFAS Reporting Rule?
California Bans PFAS in Apparel, Textiles, Cosmetics
‘The Outdoors’ Are Urban, Too
Q&A with Rachel Felder, a naturalist at the City of Detroit Parks and Recreation Department
The Outdoor Foundation’s Thrive Outside Initiative is a national network of partners working to create a more inclusive and accessible outdoor experience for all. In this Impact Stories series, we talk to local Thrive Outside leaders to learn more about their community and their vision for the future.
For a prime example of how powerful collective impact can be, Thrive Outside Detroit is a community-led network involving organizations from local, city, state, and national levels—and has already directly led to events engaging hundreds of youth in nature-based activities.
We asked Rachel Felder, a naturalist with the City of Detroit Parks and Recreation Department, about the coalition’s programming, goals, and efforts to redefine the way people see the “outdoors.”

What kind of programming are you doing through Thrive Outside?
We have nature programming throughout the city and do a lot of work focusing on bridging the gap between nature and people. Recently, we had a three-day event to celebrate National Thrive Outside Day with the Canoemobile from Wilderness Inquiry in Minnesota. We collaborated with a lot of different partners, including the Detroit Riverfront Conservancy, the U.S. Forest Service, the Belle Isle Nature Center, the U.S. Fish & Wildlife Service, and the Detroit Public Schools Community District. We were able to get probably 200 youth out paddling on the Detroit River and learning about the environment surrounding it. It was a really great opportunity to uplift and amplify what the goals of Thrive Outside are. These three days came out of multiple meetings with community partners and getting together to figure out how to have an opportunity like this for youth within the city.
How do you define the “outdoors” in an urban environment like Detroit?
We’re really trying to emphasize that there’s no wrong way to be outside, as long as you’re respecting the Earth and the people around you and you’re being safe. It doesn’t have to be this extensive experience, if you don’t want it to be. Some of us don’t necessarily feel comfortable or are not used to doing certain activities outside, and outside isn’t something that’s normalized for us. So it just starts out with talking with people.
We have a lot of pocket parks, actually. We’re working on a grant from the National Parks & Recreation Association, through the City of Detroit Parks and Rec Department, to create seven new pocket parks. We’re working with community leaders in seven districts to figure out what they want and need in their communities, and help them build it.
There are so many ways to exist in nature, and nature itself is not going to judge you for the way you want to interact with it. In every experience, we’re trying to bring people to nature, and we’re also trying to bring nature to people.
What are some ways we can make the outdoors more inclusive and accessible?
Nature is a human right, so to speak. It’s important to be talking about all of these things with people and encouraging them to utilize the natural spaces they have in their area, and just to sit outside is a great thing to do. We try to encourage them, like, “Hey, try to do some of the activities you do inside, outside.” Like reading a book, or drawing a picture, or having a simple conversation. Sometimes, shifting things outside can shift the entire dynamic of what’s being done, like having a meeting outside versus inside can be transformational.
How are you finding and engaging people to interact with your programming?
There’s a mix of us doing outreach, and people seeking and finding us. We interact with a lot of people through our social media accounts. That is where we promote many of our events. But we find that a lot of people find out about us through word of mouth. We really try to engage with many organizations within the city of Detroit to spread the word that there are opportunities to get youth and adults of color outside and camping. We have camping leadership trainings for all experience levels. Once you’ve done the training, you have access to our gear library.
One of the reasons the Thrive Outside initiative is so cool and important to us is because we love partnership. One of my colleagues likes to say that there’s so much knowledge held within people, so through working with different organizations, through working with different people, it’s really cool and powerful to be able to meet people who want to do things with us and reach out and collaborate.
How does the collective impact model relate to the work you’re doing?
The collective impact allows for organizations to come together and figure out how to collaborate. Like, you’re having this program; how can we uplift it? It’s beautiful. It brings so many people into a space to have conversations that aren’t stagnant—they’re active conversations that result in plans and partnerships and long-term relationships. We’re already collaborating on a daily basis with other organizations, like Detroit Parks and Recreation employees, YMCA employees, and Sierra Club employees — and that’s just within our Detroit Outdoors collaborative. A lot of our missions align—at the end of the day, we want to get people outside, so let’s figure out how to do it together.
Having national partners, state-level partners, city-level partners, and people on the ground in grassroots organizations, all at the same table, is something unbelievable. Seeing the engagement that comes out of these conversations and the work that Thrive is uplifting is very powerful.
How have the outdoors been impactful to you in your own life?
Detroit Outdoors took me on my first camping trip when I was 16. It’s a really full-circle experience to be taking youth even younger than me on their first camping trips, and sharing those experiences with them and knowing some of the emotions they’re having. It’s great to see their faces when they see the stars at night, or when they see a deer that they don’t expect to see. Nature is somewhere that I find a lot of peace.
What does success look like? What do you want to see Detroit achieve through Thrive Outside and beyond?
It starts with knowing what people want to do. Our gear library has been a game changer in many ways because it’s allowed us to really bridge that gap. If we’re talking about 5, 10 or even 50 years down the line, I’d like to see so many gear libraries in recreation centers and community hubs throughout the city of Detroit. If people want to go camping or skiing or canoeing, they’ll have the ability to access a gear rental system where people are keeping equipment in great condition because they know other people are using it, too.
We have a lot of vacant lots in Detroit and I think there’s a lot of potential there, as well, to make use of what we have. Some people have installed shipping containers to create useful, recreational spaces in empty lots. We ask a lot of questions about how we can give people infrastructure and resources to utilize the spaces that they have. I’d love to see more of this—maybe shipping containers with access to laundry facilities or clothes libraries so people can have gear in the winter. I’d like to see hubs for nature programming, living trailers or tiny houses where people can borrow binoculars and access passive programming in the outdoors. I want to see more free libraries and creative reading nooks with ample lighting, just creating spaces to make people want to go outside and not have to question themselves. I want it to be accessible: all body types, all learning and physical abilities. I want to see people interacting with parks in so many different ways, whether it’s reading a book or doing ecology work or citizen science, or going camping. I just want people to feel comfortable going outside and to know that they have a right to be there.
2023 Special Report on Fishing
Connecting Families with Nature is the Key to Long-Term Engagement
Q&A with Christian Vargas
Director of Community Engagement for Thorne Nature Experience
The Outdoor Foundation’s Thrive Outside Initiative is a national network of partners working to create a more inclusive and accessible outdoor experience for all. In this Impact Stories series, we talk to local Thrive Outside leaders to learn more about their community and their vision for the future.
Boulder County may have a heavy concentration of professional outdoor athletes and outdoor industry brands, but it still has a lot of work to do to make its outdoor access more equitable. Thorne Nature Experience, the backbone organization of Thrive Outside Boulder/Denver, is working to deepen families’ relationships with the outdoors—and each other—in Lafayette and beyond.
We asked Christian Vargas, the organization’s director of community engagement, what to expect from the partnership.
What are Thorne’s main goals for the Thrive Outside partnership?
We want to ensure that all of our programs are meaningful for community members and remove any barriers to participation. In addition, we want to connect youth to nature through a continuum of pre-K to high school, backyard to backcountry, and family-integrated programming.
We’re trying to work together to create meaningful engagement with the outdoors for both children and families, so that engagement is more sustainable in the long run. We understand that kids’ whole families, including the parents, siblings, aunts and uncles, and grandparents, also need to experience and have access to the outdoors in a way that is meaningful to them.
We’re trying to ensure that access to nature is more equitable in our community, so we deliver nature programs to underserved youth in the cities of Lafayette and Boulder. We’re also trying to make sure that we support their families, too, and remove any barriers to accessing nature. So, for example, the school district has a program where fourth and fifth graders go on an overnight trip to camp in the mountains. Thorne Nature Experience and Nature Kids/Jovenes de la Naturaleza has summer programs that connect the rest of the family to a similar experience with family camps throughout the year in addition to other youth programs. By providing a way for the whole family to enjoy these nature experiences, we hope that they will continue their connection with nature and keep exploring the outdoors as a family.
How are you working to increase outdoor access locally?
One of our goals is that we want to ensure that Lafayette youth are living within a safe, 10-minute walk to nature—from their home to an open space, park, or trail. Every year we strive to have meaningful programming to connect youth and their families with outdoor opportunities. Three years ago, for example, Nature Kids was able to advocate and collaborate to raise funds to build a park right next to a school where we have one of the biggest Latinx communities. The park was designed with a trail that connects with parts of the community and the local town to connect families to nature. The park has a playground with boulders, tree logs, water features, and a shelter for community use.
With so much wilderness and nature in Colorado, why is it so important to create urban green spaces?
There are some families that don’t have access to a car, or maybe they have to work really long hours that don’t allow them to do these things. Especially with COVID, I think it’s really important for families to have local access to nature that doesn’t require driving. Even if they have a car, they might not have the confidence to drive in the mountains, especially if road conditions could get bad. Then they can still walk close by and have the opportunity to access nature without other means of transportation. We know that a family that visits or shares the outdoors together will be healthier overall. Families that have time to connect with nature likely have better communication with the kids, better mental health, physical health, and lifestyle balance. So I think it’s important to also have access within the city in a way that you can easily walk to the park or a trail, and you don’t need to use a car or spend more time traveling to be in nature.
How are the outdoors meaningful to you?
When I was growing up in Costa Rica, one of the main sources of income was tourism. In the late 70s, Costa Rica started putting together land to make national parks. Now, it is one of the countries with the largest percentage of protected areas in the world—25 percent of its land is protected. Growing up there, that was one of the things we used to do—traveling a lot, going to a national volcano or one of our beautiful beaches. That’s part of the culture, to drive on the weekends to explore the outdoors or go for a hike. When I moved to Boulder, I saw how similar it was, but at the same time, different. It’s a beautiful place, with many mountains, and it snows, so you have a variety of year-round outdoor activities. That alone connects you with nature, and many of these activities, like hiking, are free. Now that I have a family, I’m trying to pass along that love for the outdoors to my family and also take advantage of all the gems here in this state.
Your kids have previously participated in some of Thorne’s programming. How did that experience impact them?
My oldest kid did a summer camp where they went to four or five different places. They started with Cal-Wood, an outdoor engagement program, in Boulder, then from there they did an overnight. It was about a week long. They learned some outdoor educational skills, they did rafting and mountain biking, and then they went into the mountains for some camping. They engaged the kids in a way that also makes it super fun, so when he came back, he was very excited—the first thing he told me is that it was super fun and he had a lot of great memories, one being a competition in starting a campfire with minimal resources. He wanted to become a summer camp counselor as soon as he was old enough.
My youngest has done some summer camps as well with Nature Kids, around the Coal Creek Trail. It’s a long trail that travels along the creek through three cities: Louisville, Lafayette, and Erie. They teach the kids about the ecosystem, the plants and animals, and they keep them outside all day. It’s a really nice way to release all of their energy and connect them with the local trail system. He also attended the YMCA Camp Santa Maria in the Mountains, an overnight camp with a lot of fun activities.
During COVID, Lafayette Nature Kids provided families with small learning cohorts for students, where they were able to balance their online learning through their schools with outdoor activities. My son participated in this program and it made a big difference for him and his mental health during those difficult times.